Choosing the right VPN is important as you don’t want to end up choosing one that doesn’t protect you. As it could leave you open to being attacked or leaking out personal data that could easily identify you and the activities you are doing using a VPN.
A VPN should be able to protect against your real IP address, that is the one assigned to you by your Internet Service Provider from being revealed to any website or web service you connect to whilst using a VPN.
I use Nord VPN and this provides me fantastic protection at keeping my IP address private and away from prying eyes. So, if I’m playing an online game whilst connected through my Nord VPN, the only IP address visible is the one assigned by Nord VPN.
Here’s a screenshot of how when connected to the Nord VPN Costa Rica VPN server, what is visible from my connection publicly.
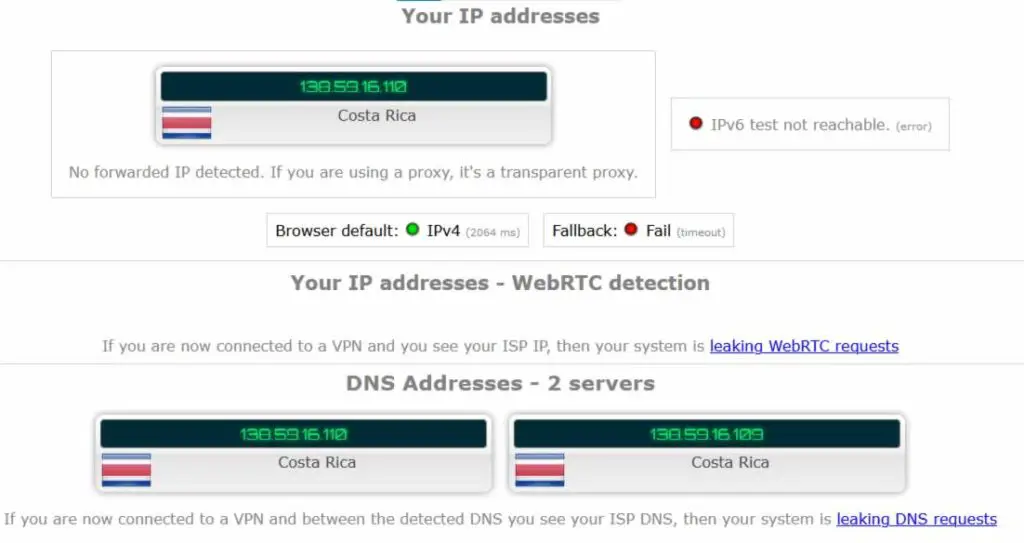
As you can see, the IP addresses are Costa Rican, that is they are the ones assigned to me by the Nord VPN server in Costa Rica. This is the IP address any website, online gaming service to even bit torrent service will see when I’m connected.
If anyone wants to find out who is using the IP address above, that is, find out my details then Nord VPN don’t keep logs and as they’re based in Panama. This jurisdiction has certain legal measures in place that make it difficult to find out which Nord VPN customers are using the Nord VPN servers across the globe.
Check out deals on Nord VPN in the link below.
Get Nord VPN special offers (up to 69% discount)
In the screenshot, the DNS servers listed are Costa Rican based, they’re actually NordVPN DNS servers to be exact. This is important as this stops the Nord VPN from leaking information, as if the DNS servers listed were those of my Internet Service Provider instead of the NordVPN DNS servers. Then my Internet Service Provider would know which websites, web services like online gaming I was using.
If I did something illegal then these websites and web services would know which Internet Service Provider I was using and could by getting a legal order, ask my Internet Service Provider to give me up. But with the DNS servers for NordVPN being listed and available to any website or web service I connect to, they would instead not know who my Internet Service Provider was.
Contacting NordVPN and requesting my details would fall on deaf ears as NordVPN have a policy of not giving up any information on their customers. Legally there wouldn’t be much that can be done either, as NordVPN is based out of Panama.
DNS Leak Protection
DNS leaks give away your Internet Service Provider details and these can then be used to find out your details by working in conjunction with the Internet Service Provider. The DNS service provided by your Internet Service Provider makes it possible for the website, the online gaming or other internet-based service to be accessible.
As you can see from the screenshot below, the Costa Rican VPN DNS details are being shown meaning NordVPN is protecting me against DNS leaks.

Everything on the internet has an address, this address is a bunch of numbers called an IP address. When you type in a website name into your browser, the name you type in must be translated into an internet address and this is what the DNS servers do. They have a list of mappings, where the name of the website or internet service is listed along with the corresponding IP address.
Once the IP address is determined, it become easier to move traffic from your location to the website or internet service. As there are special devices on the internet called routers, that can be used to send information from your computer to wherever you’re connecting to, like a website. Likewise, the routers also route information sent back to your computer from where you’ve made your connection.
When you use a VPN, a good reputable VPN provider, the DNS service you use when you make your connection is the one provided by the VPN provider. This makes it difficult to determine who your Internet Service Provider is, based on the DNS address being shown to the website or internet service you’re connected to.
Nord VPN provides great DNS leak protection as the screenshow earlier on shows, my real IP address is replaced by ones from the Costa Rican VPN I’ve connected to.
WebRTC leak protection
WebRTC is used by several common web browsers for communications, including voice calling, video calling, and various types of rapid file transfers. If the VPN doesn’t include WebRTC leak prevention, which ensures that WebRTC communications only go through the VPN connection, the WebRTC communication will circumvent the VPN and go directly to its destination.
This means that the ISP or any other service on the internet where the connection to the end destination needs to travel through will log any specifics of the WebRTC communication. Anyone with power over any of these internet services, such as the government, has the ability to monitor what users are doing.
As you can see below, my IP address is not being shown as my VPN from Nord VPN is masking my real IP address and protecting me.

No log Policy
NordVPN has a no log policy and keeps no logs of its user or their activities. Your Internet Service Provider may keep track of the websites you’ve visited. ISPs retain logs on their DNS services to track their customers’ viewing behavior.
However, if a VPN is utilized, any potential logs will now surface on the VPN’s DNS servers. If you use a VPN that doesn’t retain logs, it will be impossible to monitor what websites and internet services you’ve visited. Many VPNs market themselves as being able to provide this “no logging” service as the ultimate form of privacy protection.
It’s impossible to say whether this is true for all VPNs because some VPNs have a “no logging” policy yet have provided logs when government agencies have requested them. Clearly demonstrating that they had been maintaining logs and lying about their ‘no logging’ policy in their advertising and sales materials.
My own checking with NordVPN hasn’t found this to be the case, as they have been independently audited. More importantly a malicious group did some hacking and were untraceable as they used NordVPN, making it near impossible for the government agencies to work out who the malicious group was, as there were no logs available.
Uncrackable encryption
Government agencies such as the National Security Agency (NSA) have capabilities that allow them to break through some encryption types giving them visibility to the traffic travelling between the VPN client to the VPN server at the VPN provider.
These government agencies would be able to quickly determine the websites the users have visited as a result of this. Not all VPNs use high-grade encryption, those that don’t put their clients at danger of having their privacy violated by making it easier for them to be tracked because encryption may be readily broken with the right tools.
It’s critical that any VPN you choose needs sufficient levels of encryption, ideally high-grade that hasn’t been hacked, as this will prevent the VPN from divulging what the VPN user is doing online and prove much more difficult for anyone, including the government, to track what they’re doing.
Fortunately for me, NordVPN has very strong encryption that is very difficult to crack as well as a number of settings to ensure different levels of encryption can be set depending on the VPN connection protocol chosen. Whereby, I can decide to elect even higher levels of encryption than what’s offered as default by using the NordLynx VPN protocol.
Kill Switch Protection
You’re wide open and vulnerable to being tracked if you neglect to have your VPN automatically running after deciding to log onto your computer, tablet, or smartphone because the real IP address assigned to you by your ISP is available to anything you connect to on the internet be it the websites to internet services like online gaming.
Consider if you’ve turned your VPN on, keeping it running and then left it running and gone to bed. The files you’ve set to download, carry on being downloaded but the VPN connection drops in the night?
This will not prohibit the traffic from being sent insecurely over your internet connection, and all web traffic instead carries on being sent over the conventional path to it’s destination, as it would be if you weren’t connected through a VPN.
Through switching to the conventional route, the ISP’s given IP address becomes open to the world as the VPN’s safeguards are momentarily disabled until the connection to the VPN server is restored. All activity, such as visiting websites, can now be easily traced, with the ISP knowing what their user is doing, as it keeps a log of all activities. This means that whilst the VPN connection is active then the protections offered by the VPN are in play and to make sure the VPN protections remain in place at all times during any connectivity to the VPN, a Kill switch is definitely required.
Some VPNs provide Kill Switch capability to ensure that the VPN’s protections are maintained. When the VPN connection fails, the VPN Kill Switch removes internet connectivity, effectively blocking connectivity to the internet.
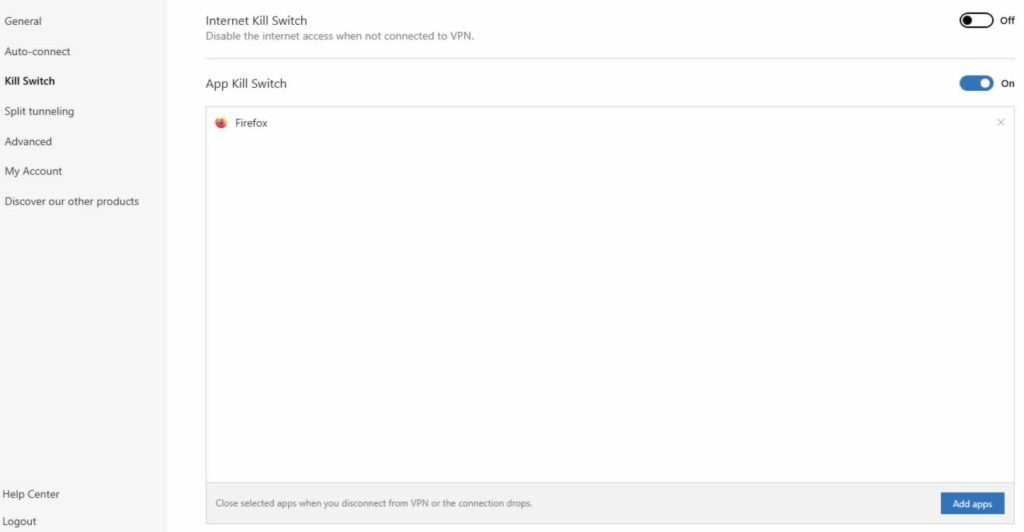
Nord VPN allows an overall Kill Switch to be enabled across the board, so any internet bound traffic will be stopped if the VPN connection drops. Or individual applications can be included like Mozilla Firefox has been included in the screenshot above.
Normally, a notice will appear, stating internet connectivity is disabled as the Kill switch has become effective when the VPN connection fails. The VPN will attempt to reconnect with the VPN server automatically and will keep trying until the connection is made. When the connection is made to the VPN server, the Kill switch will allow connections to the internet to be made again.
More than a Plugin
Using browser plugins for Mozilla Firefox or Google Chrome that provide VPN functionality, make it possible to provide some VPN protections to any browsing being done. This is done by automatically forwarding connections made to websites through a VPN server across an encrypted connection. Thereby stopping the ISP from seeing what their customers are browsing.
My only issue with these plugin VPNs is they are not full VPNs and as such won’t provide the level of protection a full VPN client will provide. As these plugins only protect web browser traffic and there’s other traffic like traffic from instant messaging apps to voice and video call apps that will not be protected by a browser plugin offering VPN services.
Not all VPN plugins are the same either, as some simply may not offer enough protection even for traffic sent to the websites being browsed on your browser. As they may have poor levels of encryption or worse still, may not even use any encryption. These plugins may also have vulnerabilities themselves which may have been hacked by malicious parties or even infiltrated by government or state agencies.
Another thing to watch out for, is that many businesses providing VPN plugins may deliberately take data like your browsing history and sell this onto other businesses or even the government in order to generate more revenue.
Malware Protection
Connecting to website and internet services could expose you to malware and viruses but with NordVPN it has this protection built in using it’s CyberSec setting.
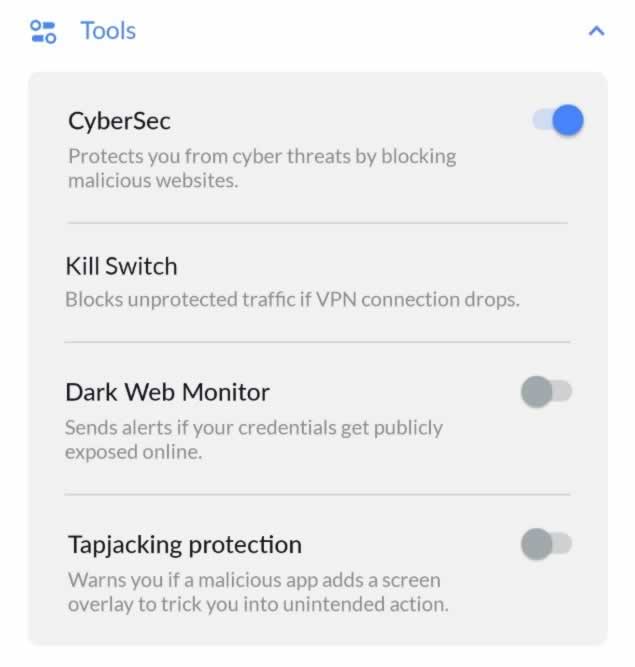
In the screenshot above, I have enabled the CyberSec on NordVPN application on my smart phone, so all VPN connections to websites will be checked to see if they are safe or not as it allows it to block access to malicious websites that may be laden with malware and viruses. Providing a welcome layer of additional protection to the anti-virus and anti-malware programs that most of us already use.
One of the other benefits of malware protection is any malware designed to work out your location or steal your personal information will be reduced in it’s capacity and become ineffective. This is important especially if you’re using the VPN to keep your identity secret as you may live in a region where information access is severely restricted.

